Results
Unfortunately, you didn’t pass the test. I recommend going back and reading through the information provided on this website, as it will aid you in staying safer while traversing the digital world. And don’t worry—there is a lot to look out for, but it is crucial to have a basic understanding of what to look out for. Keep at it!
#1. What does SSL/TLS encryption ensure when browsing websites?
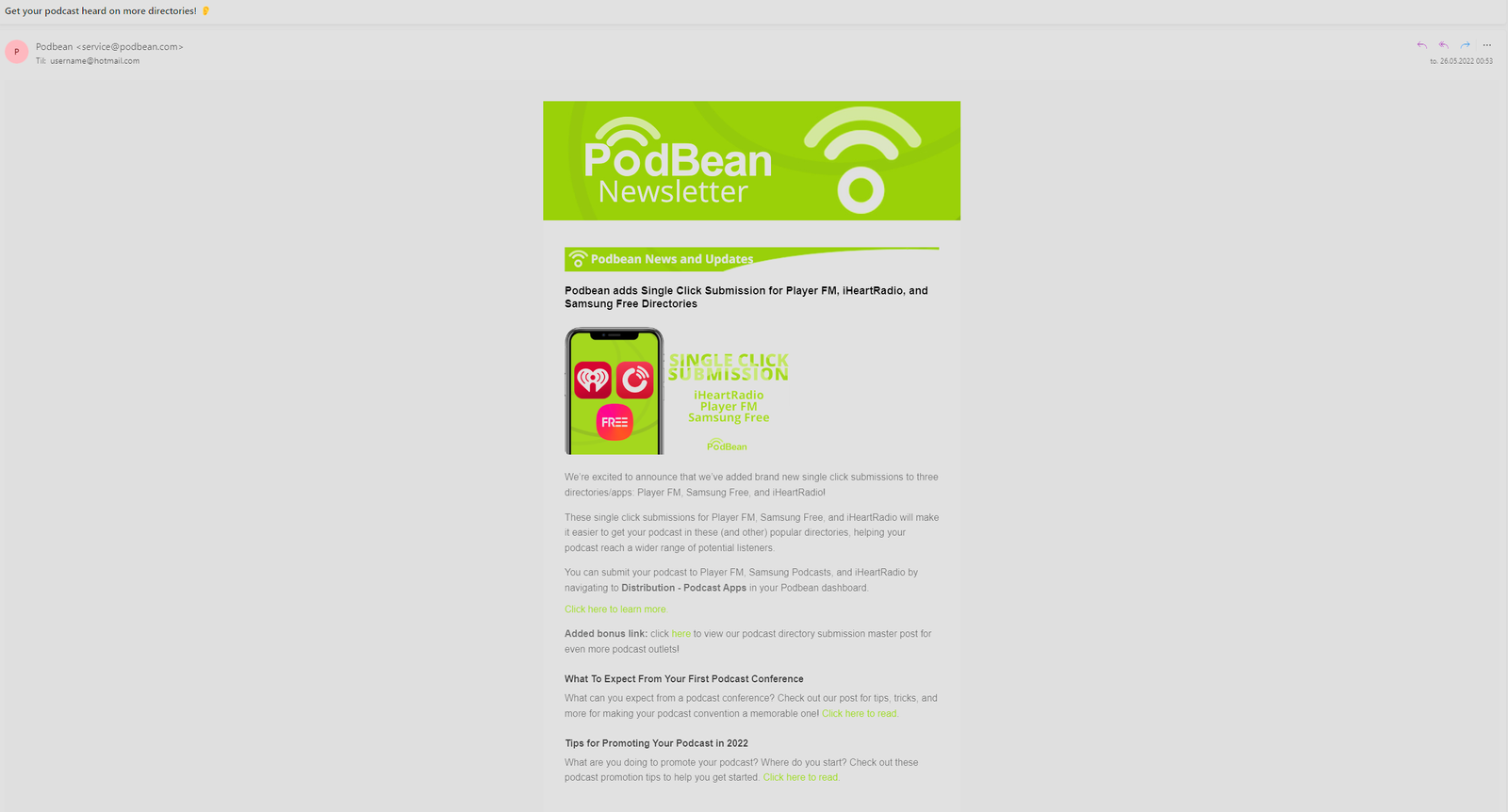
#2. Analyse the provided picture of an email and figure out if it is REAL or FAKE (Right-click the image and click Open Image in New Tab to analyse it)
This is just a comercial email that is advertising for PodBean. Going thorugh the checlist of what to look for we see:
Sender address: service@podbean.com which is a legit email address for podbean.
The content: The language and sentence structure seems to be good.
Link: There are quite alot of links, this can be expected from some comercial emails that is trying to sell you their product.
#3. What is the importance of incident reporting?
Select all that apply:
The correct answers are
It helps to notify relevant platforms about security breaches or cyberattacks
It decreases the chances of others encountering malicious content
Reporting incidents is crucial because it allows authorities and platforms to take action promptly, stopping cyber threats in their tracks and safeguarding internet users from harm.
#4. What long-term effects can frequent reporting of phishing scams have?
Select all that apply:
The correct answers are
It can lead to email providers flagging the scams as phishing and blocking them
it can lower the frequency of phishing scams appearing in your inbox
By frequently reporting scam emails, the email provider (Gmail, Outlook, and others) can block them, which means they won’t reach your inbox anymore.
#5. What is a common tactic used in phishing emails to prompt quick action?

#6. Analyse the provided picture of an email and figure out if it is REAL or FAKE (Right-click the image and click Open Image in New Tab to analyse it)
This is a fake email or a scam. First we see the email address is quite lenghty and seemingly randome. Then we see they are playing on greed, click here to win 100 bucks. Lastly, there is no context or anything other than links to click on and the little text there is not really good english.
#7. What role do antivirus software and firewalls play in device security?
#8. What is the purpose of setting up a PIN or password for your device?
#9. Describe the term used to refer to the process of converting plaintext data into an unreadable format to prevent unauthorised personel reading it.
#10. What action should you take if you suspect an email is a phishing attempt?
#11. Why is it important to lock your devices when not in use?
#12. What is a recommended practice for securing physical documents when not in use?
#13. How can you ensure the safety of sensitive documents before leaving or disposing of them?
Select all that apply:
The correct answers are
Store them in a safe place
Shred or destroy them
Storing sensitive documents in locked drawers or other secure places makes it harder for people to access the information. The same applies to disposing of sensitive documents; if they are destroyed before being thrown away, others can’t recover the information.
#14. Why is using the same password across multiple accounts considered risky?
Select all that apply:
The correct answers are
If one account is compromised, all linked accounts become vulnerable. If one account becomes compromised, meaning someone knows your login credentials, and you use the same login everywhere, it’s easy for the person who has your information to log in to other accounts as well.
It improves account accessibility. It improves account accessibility not only for you but for malicious actors as well.